What is the difference between Forward Proxy vs Reverse Proxy?
Understand, The role that proxies play in web architecture and consider using them to improve the performance, security, and scalability of your site.
In today's world, where security breaches and cyberattacks are prevalent, the use of proxies has become essential for businesses and organizations. Proxies can offer protection, enhance privacy, and improve performance.
Forward and Reverse proxies are two types of proxies that are commonly used in different scenarios. In this article, we will explore the differences between forward proxy vs reverse proxy and the benefits of using them.
1. What is a Proxy?
A proxy server acts as an intermediary between a client and a server, forwarding requests from clients to servers and responses from servers to clients. A proxy server can be used for various purposes, including:
- Improving performance by caching web pages and reducing the number of requests sent to servers.
- Enhancing privacy by hiding the IP address and other identifying information of the client.
- Filtering content by blocking access to specific websites or content based on predefined rules.
- Providing security by inspecting traffic and blocking malicious requests.
Now that we have an understanding of what a proxy server is and its purpose, let's explore the differences between forward proxy vs reverse proxy.
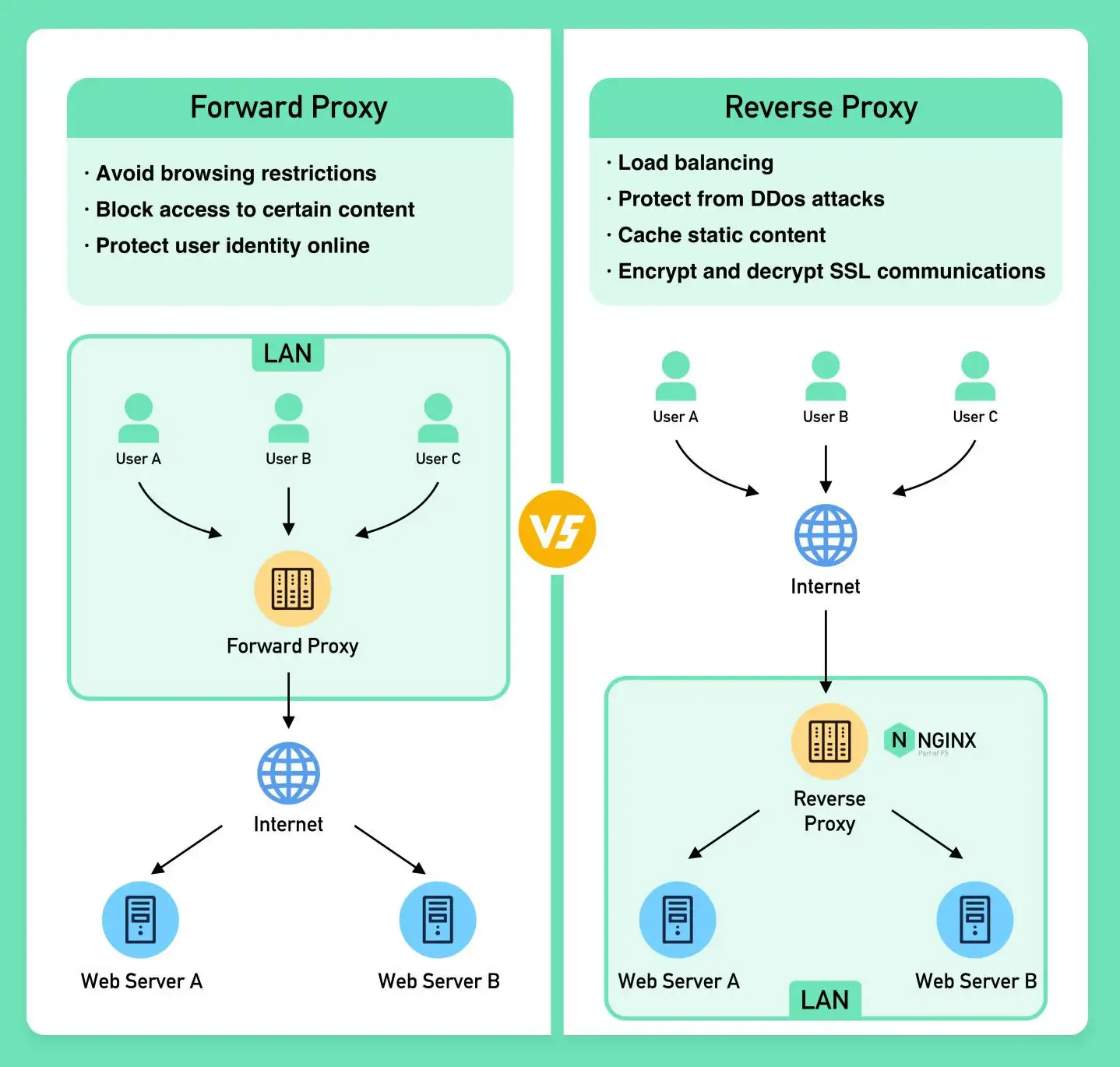
2. What is a Forward Proxy?
A forward proxy, also known as an HTTP proxy, is a server that sits between a client and the internet. When a client makes a request to access a website, the request is first sent to the forward proxy, which then forwards the request to the website. The website then sends a response to the forward proxy, which in turn forwards the response back to the client.
A forward proxy is commonly used by individuals and organizations to access the internet anonymously, bypass web filters, and improve performance by caching frequently accessed content. For example, a company might use a forward proxy to allow its employees to access the internet while hiding their IP addresses and blocking access to certain websites.
2.1 How Does a Forward Proxy Work?
When a client requests a resource through a forward proxy, the request is intercepted by the proxy server. The proxy server then forwards the request to the target server, retrieves the requested resource, and then sends it back to the client. This process creates an additional layer of security and can protect the client from attacks like DDoS, as the target server only sees the proxy server's IP address.
2.2 Where Forward Proxy is used?
Forward proxies are used in various scenarios, including:
- Security: Forward proxies can be used as a security measure to protect the internal network by preventing direct access to it. In this case, the forward proxy is placed in a demilitarized zone (DMZ) and all incoming requests are forwarded through it to the internal network.
- Caching: Forward proxies can also be used as a caching mechanism to improve performance by storing frequently accessed resources locally. This can reduce the response time for subsequent requests and also reduce the load on the origin server.
- Access control: Forward proxies can be used to restrict access to certain websites or services. This is often used in corporate environments where certain websites or services are blocked for security or productivity reasons.
- Anonymity: Forward proxies can be used to provide anonymity by masking the IP address of the client making the request. This is often used by individuals who want to protect their privacy or bypass geographical restrictions on certain websites or services.
- Content filtering: Forward proxies can be used to filter content based on certain criteria, such as keywords or file types. This can be used to block access to certain types of content, such as adult material or copyrighted content.
3. What is a Reverse Proxy?
A reverse proxy, also known as an HTTP accelerator, is a server that sits between a client and a web server. When a client makes a request to access a website, the request is first sent to the reverse proxy, which then forwards the request to the web server. The web server then sends a response to the reverse proxy, which in turn forwards the response back to the client.
A reverse proxy is commonly used by organizations to improve performance, increase security, and distribute traffic across multiple web servers. For example, a company might use a reverse proxy to load balance traffic across multiple web servers to ensure that no single server is overloaded. A reverse proxy can also be used to protect web servers from direct access by hiding their IP addresses and blocking malicious requests.
3.1 How Does a Reverse Proxy Work?
When a client sends a request to a server through a reverse proxy, the proxy server intercepts the request and decides which server to forward the request to. The proxy server then retrieves the resource from the chosen server and sends it back to the client. This process can improve website performance and protect the server from attacks like DDoS.
3.2 Where Reverse Proxy is used?
Reverse proxies are used in a wide range of applications, including:
- Load balancing: Reverse proxies can distribute incoming traffic among multiple backend servers, helping to ensure that no single server is overwhelmed with traffic. This can help improve the availability and performance of web applications.
- Web acceleration: Reverse proxies can cache frequently requested content, such as images, CSS files, and JavaScript files. By serving these files from cache, rather than making multiple requests to the backend servers, reverse proxies can help improve the speed and performance of web applications.
- Security: Reverse proxies can act as a barrier between the public internet and a web application, helping to protect against attacks such as DDoS attacks, SQL injection, and cross-site scripting (XSS) attacks. Reverse proxies can also help enforce security policies, such as requiring HTTPS connections.
- Content filtering: Reverse proxies can filter incoming traffic based on a variety of criteria, such as IP address, user agent, and content type. This can be useful for blocking malicious traffic, or for restricting access to certain types of content.
- Geolocation-based content delivery: Reverse proxies can use geolocation information to serve content to users based on their location. This can be useful for delivering localized content, such as language-specific versions of a website, or for serving content that is subject to geographic restrictions.
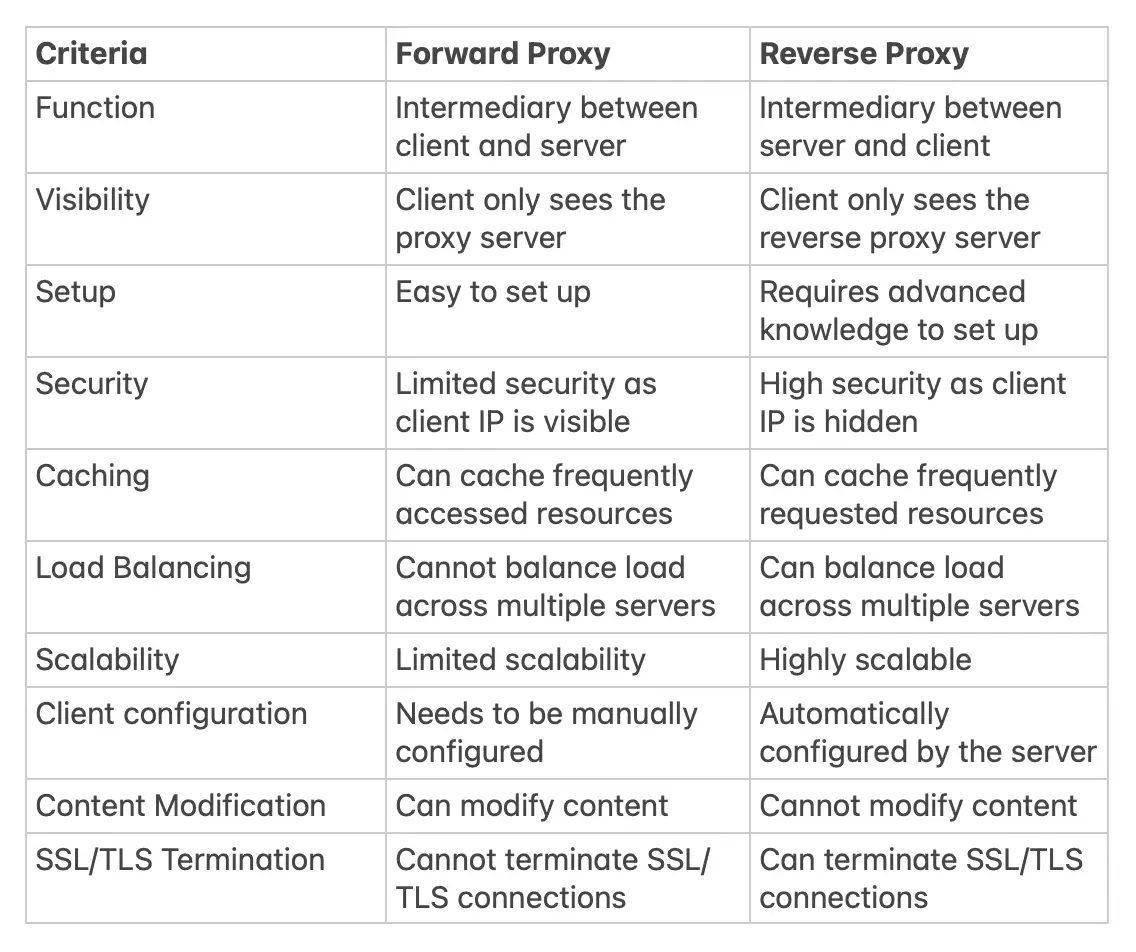
4. Forward proxy vs Reverse Proxy
Key Differences
| Characteristics | Forward Proxy | Reverse Proxy |
|---|---|---|
| Placement | Client Side | Server Side |
| Functionality | Filters outgoing requests from clients | Filters incoming requests from clients |
| User Awareness | Client can be aware of the existence of the forward proxy | Client is unaware of the existence of the reverse proxy |
| Network Flow | Client makes request to the forward proxy, then forward proxy makes request to server | Client makes request to reverse proxy, then reverse proxy forwards request to server |
| Encryption | Can be used to encrypt traffic between client and proxy | Can be used to encrypt traffic between proxy and server |
| IP Spoofing | Can be used to spoof the client's IP address to the server | Does not support IP spoofing |
| Caching | Can cache frequently requested content | Can cache frequently requested content |
| Load Balancing | Cannot be used for load balancing | Can be used for load balancing |
| Security | Can be used to filter malicious traffic | Can be used to filter malicious traffic |
| Application Support | Can be used for HTTP, FTP, SMTP, and other protocols | Can be used for HTTP, HTTPS, SMTP, and other protocols |
| Configuration | Must be configured on the client side | Must be configured on the server side |
| Scalability | Does not scale well for large networks | Scales well for large networks |
| Performance | Can cause latency due to the additional hop | Can improve performance by caching and load balancing |
| SSL Inspection | Cannot inspect encrypted traffic | Can inspect encrypted traffic |
| Server Management | Does not require server management | Requires server management |
| Access Control | Can be used to control access to specific websites or content | Can be used to control access to specific websites or content |
| Resource Protection | Cannot be used to protect servers from DDoS attacks | Can be used to protect servers from DDoS attacks |
| Content Filtering | Can be used to filter content based on policy | Can be used to filter content based on policy |
| Protocol Support | Supports client-side protocols only | Supports server-side protocols only |
| Client Configuration | Must be configured on each client | Clients do not need to be configured |
#1. Forward Proxy:
- A forward proxy acts on behalf of a client and makes requests to servers.
- The client is aware of the forward proxy and sends requests to it.
- The server is not aware of the client but instead receives requests from the forward proxy.
- It is commonly used to control access to the internet for internal networks.
- A forward proxy can be used to access geographically restricted content, such as streaming services and social media platforms.
- For example, a company may use a forward proxy to restrict employee access to specific websites during work hours.
- 7. A forward proxy is configured on the client side, and all requests from the client are directed through the proxy.
- The IP address of the client is hidden from the server, which sees only the IP address of the proxy.
- It is commonly used to filter and block access to specific websites based on organizational policies.
- A forward proxy can also be used to accelerate browsing by caching frequently accessed content.
- For example, a school may use a forward proxy to prevent students from accessing inappropriate websites.
- 17. A forward proxy can be used to bypass internet restrictions and access censored content in some countries.
- It can also be used to maintain anonymity and protect privacy when browsing the internet.
- A forward proxy can be configured on individual devices or on a network level.
- For example, a journalist reporting from a country with internet censorship may use a forward proxy to access censored content without being traced.
#2. Reverse Proxy:
- A reverse proxy acts on behalf of a server and makes requests to clients.
- The client is not aware of the reverse proxy and sends requests to the server.
- The server is aware of the reverse proxy and sends responses to it, which the proxy then sends to the client.
- It is commonly used to provide load balancing and caching for web servers.
- A reverse proxy can also be used for security purposes by hiding the internal network structure.
- For example, a website with multiple servers may use a reverse proxy to distribute incoming requests among the servers to balance the load.
- 12. A reverse proxy is configured on the server side and intercepts incoming requests before they reach the server.
- The IP address of the client is visible to the server, but the server's IP address is hidden from the client.
- It is commonly used to distribute traffic among multiple servers to improve performance and scalability.
- A reverse proxy can also be used to add security features like SSL encryption and authentication.
- For example, an e-commerce site may use a reverse proxy to handle incoming requests and route them to multiple servers to prevent downtime during high traffic periods.
- 21. A reverse proxy can be used to prevent direct access to servers by hiding their IP addresses.
- It can also be used to filter and block incoming traffic based on IP address, geographical location, or other criteria.
- A reverse proxy can be configured to handle multiple domains and subdomains on a single server.
- For example, a company may use a reverse proxy to provide access to multiple web applications hosted on different servers.
5. Why Reverse Proxies (NGINX)
Are Important for Modern Websites
NGINX is a popular web server software that is known for its high performance, scalability, and reliability. It is commonly used to serve static content, handle SSL encryption, and act as a reverse proxy.
1. Protection Against DDoS Attacks
A reverse proxy can be used to protect a website from Distributed Denial of Service (DDoS) attacks. The website's IP addresses are hidden behind the reverse proxy, making it harder for attackers to target the web servers directly. By distributing incoming traffic across a large pool of web servers, the reverse proxy prevents any single server from becoming overloaded.
2. Load Balancing
A reverse proxy is used for load balancing to distribute incoming traffic across multiple web servers. A popular website handling millions of users every day is unlikely to handle the traffic with a single server. A reverse proxy can balance a large amount of incoming requests by distributing the traffic to a large pool of web servers, effectively preventing any single one of them from becoming overloaded.
3. Caching Static Content
A reverse proxy can cache static content, such as images, scripts, and stylesheets, for a period of time. If the same piece of content is requested again from the reverse proxy, the locally cached version can be quickly returned. This reduces the load on the web servers and improves the website's performance.
4. Handling SSL Encryption
SSL handshake is computationally expensive. A reverse proxy can free up the origin servers from these expensive operations. Instead of handling SSL for all clients, a website only needs to handle SSL handshake from a small number of reverse proxies.
Layers of Reverse Proxy
The first layer of reverse proxy is often provided by edge services such as Cloudflare. These edge services provide reverse proxy servers that are deployed to hundreds of locations around the world, close to the users. By placing these servers close to the users, edge services can reduce the latency and improve the response time of websites.
The second layer of reverse proxy is often provided by an API gateway or load balancer at the hosting provider. This layer of reverse proxy is responsible for distributing incoming traffic to a pool of web servers. Load balancers ensure that incoming requests are evenly distributed over a cluster of web servers. They can also perform health checks on the web servers to detect failures and automatically remove them from the pool of available servers.
Many cloud providers combine the edge service and the API gateway or load balancer into a single ingress service. Users enter the cloud network at the edge close to the user, and from the edge, the reverse proxy connects over a fast fiber network to the load balancer, where the request is evenly distributed over a cluster of web servers.
Each layer of reverse proxy adds more complexity and provides additional features to improve the performance, security, and scalability of websites. However, it's important to note that each layer also introduces additional latency and potential points of failure. Website owners must carefully consider the tradeoffs between complexity and performance when deciding on the number and configuration of reverse proxy layers.
FAQs
What is the difference between a forward proxy and a reverse proxy?
The main difference is the direction of the traffic flow. A forward proxy is used by clients to access servers, while a reverse proxy is used by servers to access clients.
What are the benefits of using a forward proxy?
A forward proxy can help increase security and privacy, reduce network traffic, and provide caching and content filtering.
What are the benefits of using a reverse proxy?
A reverse proxy can help improve performance, scalability, availability, and security.
What is load balancing?
Load balancing is the process of distributing network traffic across multiple servers to ensure optimal performance and availability.
How does a reverse proxy help with load balancing?
A reverse proxy can distribute traffic across multiple servers based on a set of rules, such as round-robin, least connections, or IP hashing.
What is caching?
Caching is the process of storing frequently accessed data in a cache to reduce the number of requests to the original source.
How does a forward proxy help with caching?
A forward proxy can store frequently accessed data in a cache to reduce the number of requests to the original source and improve performance.
How does a reverse proxy help with caching?
A reverse proxy can store frequently accessed data in a cache to reduce the number of requests to the server and improve performance.
What is SSL termination?
SSL termination is the process of decrypting SSL traffic at the proxy and forwarding it to the server in plain text.
How does a reverse proxy help with SSL termination?
A reverse proxy can terminate SSL connections on behalf of the server, reducing the processing load on the server and improving performance.
What is a DMZ?
A DMZ, or demilitarized zone, is a network segment that is isolated from the internal network and exposed to the public internet.
How does a reverse proxy help with DMZ security?
A reverse proxy can act as a gateway between the DMZ and the internal network, reducing the attack surface and improving security.
What is content filtering?
Content filtering is the process of blocking access to certain types of content based on a set of rules, such as URLs or keywords.
How does a forward proxy help with content filtering?
A forward proxy can block access to certain types of content based on a set of rules, helping to enforce corporate policies and improve security.
How does a reverse proxy help with content filtering?
A reverse proxy can block access to certain types of content based on a set of rules, helping to improve security and protect against malicious traffic.
What is an API gateway?
An API gateway is a type of reverse proxy that provides a single point of entry for multiple APIs, allowing for unified authentication, rate limiting, and routing.
How does a reverse proxy help with API management?
A reverse proxy can act as an API gateway, providing a centralized point of control for multiple APIs and improving security, scalability, and performance.
What are some common use cases for reverse proxies?
Common use cases for reverse proxies include load balancing, caching, SSL termination, DMZ security, and API management, among others.
